ARGUS Detections
Argus and Detections
Argus is a network activity audit facility, generating status records on the existence, and status of network transactions. This data contains features that can be used to perform a large number of network operations and cyber security detections.
Detections can be very simple for a network flow system, such as the attempt to connect to a known bad actor. If you have a list of bad IP addresses, it can be a cheap and simply filter match to see who is trying to connect or is successfully connecting to a bad actor.
Detections can also be highly technical and complex, such as the occurence of keystrokes in an http connection to an external unfamiliar IP address just after a reference to a host that was learned using an fully qualified domain name that is known to be bad.
Argus's data model contains most of the data that is used by intrusion detections systems such as Snort, to pattern match against known signatures for potential bad actor behavior. And its ability to capture portions of the packet payloads can support limited Deep Packet Inspection strategies.
Combining these detection techniques against a lot of network history enables you to do something that is pretty hard in todays networks; detect instances of cyber security problems that occurred in the past.
If your Argus data is well developed, stored and conditioned, you should be able to accomplish a new family of security capabilities using argus data and argus client programs.
Integrated Detections
The Argus open source sensor has integrated analytics that are designed to reveal specific indicators of behavior that can only be detected in the Argus sensor itself. These features can be used to detect very sophisticated network based attack strategies.
Keystroke Detection
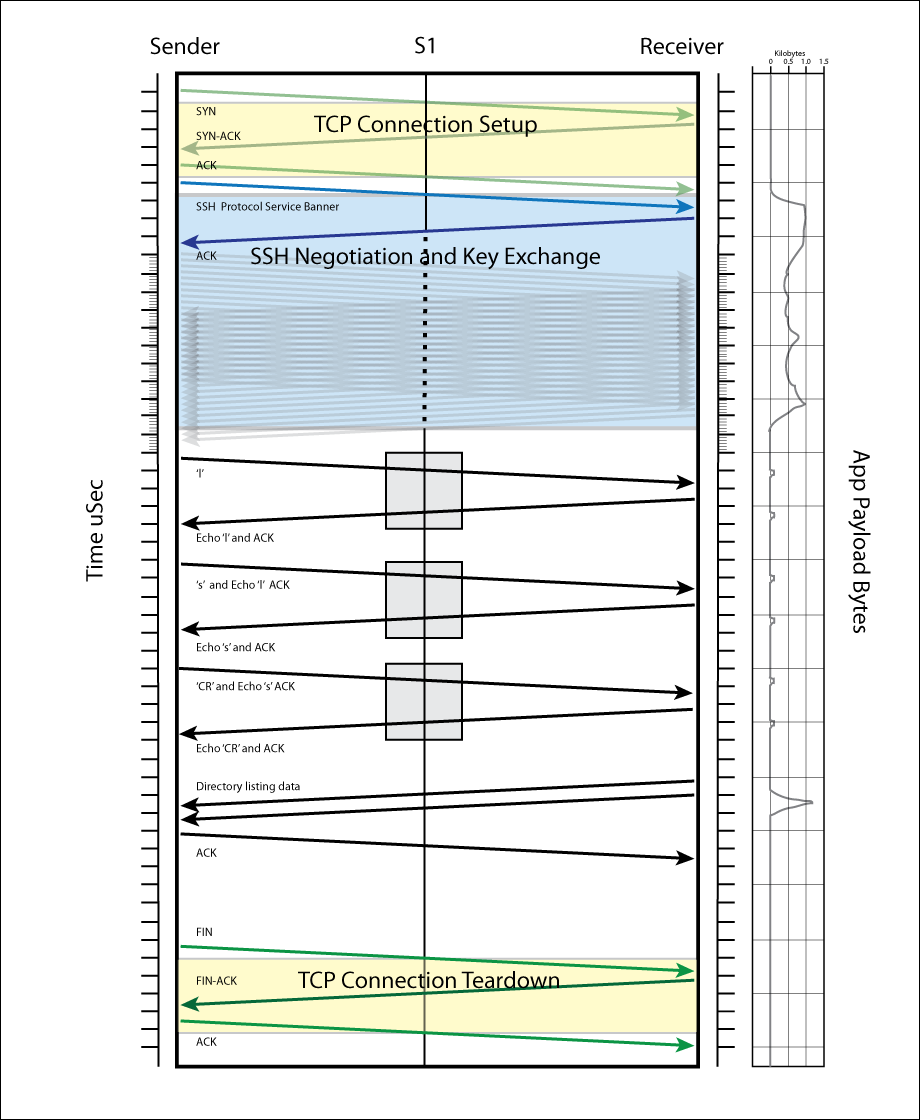
Argus has within its packet dynamics engine, a machine learning based detection model that identifies potential keystrokes in encrypted network streams. Based on a collaboration between Purdue University, Stanford University and the Argus Project (QoSient) in 2010, we implemented an integrated analytic designed to detect behavior in SSH traffic, and extended that to any TCP based communication.
Having the count of potential keystrokes is a great start to recognizing any form of remote access terminals (RATs) in any traffic.
Fragmentation Overlap Detection
One of the first integrated behavioral detections implemented in Argus was to monitor IP Fragments, to see if there were re-assembly bugs and performance problems in IP stacks. At the CERT, we researched the potential for IP fragments to present a problem to firewalls, and the result was an integrated detection feature when Argus saw fragment overlapping, where a IP fragment wrote over the contents of a previous packet. This type of behavior is a direct indication of packet protocol manipulation, and is still today a very serious (nation state level) indication of intrusion.
Reputation Based Detection
The Argus open source distribution has client programs that can match flow data against 3rd party intelligence data, like Emerging Threats and Firehol. Simple programs like rafilteraddr.1 can read the lists of IP addresses from these intelligence sources and test flow records against very large lists of IP addresses, either in real-time, or against stored data for a retrospective detection. While these tools are rather simple, they can be integrated into more complex processes that create very sophisticated detection schemes.
Argus has a specific 6-tuple flow model for DNS traffic, which enables argus flow data to capture the complete DNS transaction. Collect all of the DNS transactions off the wire, and you have a great opportunity to do a number of cyber detections. As an example, with this data and programs like radns.1, you can detect if entities in your network lookup names from 3rd party intelligence lists, in either real-time or historically.
The open source project currently has prototype programs to do the basics, and the data enables development of the most sophisticated of detections.

Title

Title

Title
Behavioral Anomaly Detection
The key to behavioral anomaly detection is to have a concise method of defining normal behavior, and a simple means of comparing behaviors over time. Argus is all about network summarization. The sensor generates summarizations of packets and their contents, and the client tools provide summarizations of flow data records through aggregation. When you use the tools to generate hourly, daily, weekly, monthly, annual or life-time summarizations, you are beginning to walk down the path toward effective behavioral anomaly detection.
Argus has been used at a number of US Gov't and University sites to develop persistent behavioral baselines of network activity. Tracking simple metrics such as the total number of bytes, or the total ingress packets or the number of hosts that an endpoint talks to in a day, can enable a large family of new anomaly detections.
The open source code provides the basic data and methods needed to develop any number of complex behavioral baselines, and to generate simple statistical indicators of change.
Deferred IDS
Argus data contains a large number of network traffic features that are used by IDS systems to generate security alarms and alerts. This sets up the ability for argus client programs to look for addresses, protocols and ports to detect many IDS events.
Modern IDS uses Deep Packet Inspection to look for patterns in network traffic payloads. Argus can be configured to capture selective payloads of every flow, and with a well chosen user data capture configuration, you capture enough payload data to satisfy most IDS packet content inspection requirements. We call this "shallow packet inspection".
Using these techniques, Argus can provide a full featured IDS capability, much like a Snort IDS capability, against historical Argus data. The current open source has many of these capabilities integrated into the client programs. rafilteraddr.1 can match against large numbers of IP addresses, it can perform regular expression matching on payload contents and it can pipe its output into the ralabel.1 client program that can match against large numbers of flow specifications (n tuple matches) and label the flows with specific indicators.
When new signatures are discovered, if you have a good set of historical Argus data and a good grasp of the argus client program strategy, you can look back to see if your enterprise has seen most new attack techniques.

Title

Title